The Asia Pacific Deception Technology Market would witness market growth of 13.3% CAGR during the forecast period (2024-2031).
The China market dominated the Asia Pacific Deception Technology Market by Country in 2023, and would continue to be a dominant market till 2031; thereby, achieving a market value of $368.8 million by 2031. The Japan market is expected to witness a CAGR of 12.6% during (2024 - 2031). Additionally, The India market would register a CAGR of 14% during (2024 - 2031).
The shift toward digital transformation has further underscored the importance of deception technology. As organizations embrace digital tools and platforms to enhance efficiency and innovation, their reliance on interconnected systems increases. This interconnectedness, while beneficial, also creates vulnerabilities that attackers can exploit. Deception technology helps organizations navigate this transformation securely by providing a robust threat detection and mitigation framework. It ensures that businesses can reap digitalization's benefits without compromising security.
Industries like healthcare and banking benefit greatly from deception technology in meeting industry-specific standards like HIPAA and PCI DSS. For instance, healthcare organizations can deploy decoy electronic health records (EHRs) to detect unauthorized access attempts, preventing real patient data from being compromised while demonstrating compliance. In banking, decoy payment gateways can isolate fraudulent activities, safeguarding actual financial transactions. Beyond compliance, deception technology enhances stakeholder trust by showcasing an organization’s commitment to data protection. As cybersecurity regulations evolve, the ability of deception technology to provide real-time detection and actionable intelligence ensures organizations remain compliant and resilient in an increasingly regulated and threat-prone environment.
Australia is also witnessing a surge in demand for deception technology due to its growing dependence on digital platforms and the escalating number of cyberattacks. The Australian Cyber Security Centre reported over 94,000 cybercrime incidents during the financial year, a 23% increase from the previous year. Identity-based threats like phishing and ransomware have targeted businesses across multiple sectors. To combat these challenges, the Australian government’s Cyber Security Strategy 2023 promotes national cyber resilience and encourages the adoption of advanced security solutions, including deception technology. These initiatives are anticipated to stimulate significant development in Australia's cybersecurity industry, as organizations prioritize advanced threat detection and mitigation solutions. Therefore, the Asia Pacific region’s rapid advancements in digital infrastructure and increasing cybersecurity risks position it as a key market for deception technology.
Free Valuable Insights: The Global Deception Technology Market is Predict to reach USD 4.8 Billion by 2031, at a CAGR of 12.7%
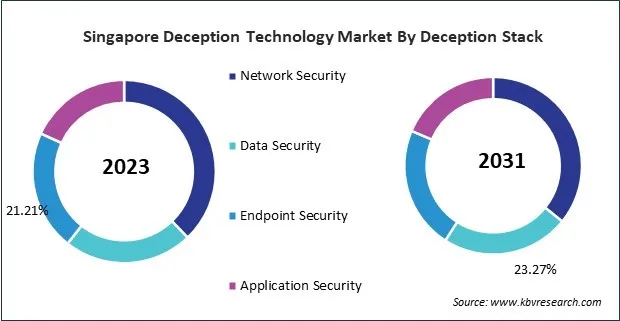
Based on Component, the market is segmented into Solutions and Services (Professional Services and Managed Services). Based on Deployment Mode, the market is segmented into Cloud and On-premise. Based on Deception Stack, the market is segmented into Network Security, Data Security, Endpoint Security, and Application Security. Based on Organization Size, the market is segmented into Large Enterprises and Small & Medium Enterprises (SMEs). Based on Vertical, the market is segmented into BFSI, Government, Healthcare, Energy & Utilities, IT & Telecom, Retail, Manufacturing, and Other Vertical. Based on countries, the market is segmented into China, Japan, India, South Korea, Singapore, Malaysia, and Rest of Asia Pacific.
By Component
By Deployment Mode
By Deception Stack
By Organization Size
By Vertical
By Country
Our team of dedicated experts can provide you with attractive expansion opportunities for your business.